AAA Configuration on NX-OS
AAA security provides the following services:
Authentication: Identifies users, including login and password dialog, challenge and response, messaging support, and, depending on the security protocol that you select, encryption.
Authentication is the process of verifying the identity of the person or device accessing the Cisco NX-OS device, which is based on the user ID and password combination provided by the entity trying to access the Cisco NX-OS device. Cisco NX-OS devices allow you to perform local authentication (using the local lookup database) or remote authentication (using one or more RADIUS or TACACS+ servers).
Authorization: Provides access control.AAA authorization is the process of assembling a set of attributes that describe what the user is authorized to perform. Authorization in the Cisco NX-OS software is provided by attributes that are downloaded from AAA servers. Remote security servers, such as RADIUS and TACACS+, authorize users for specific rights by associating attribute-value (AV) pairs, which define those rights with the appropriate user.AccountingProvides the method for collecting information, logging the information locally, and sending the information to the AAA server for billing, auditing, and reporting.
The accounting feature tracks and maintains a log of every management session used to access the Cisco NX-OS device. You can use this information to generate reports for troubleshooting and auditing purposes. You can store accounting logs locally or send them to remote AAA servers.
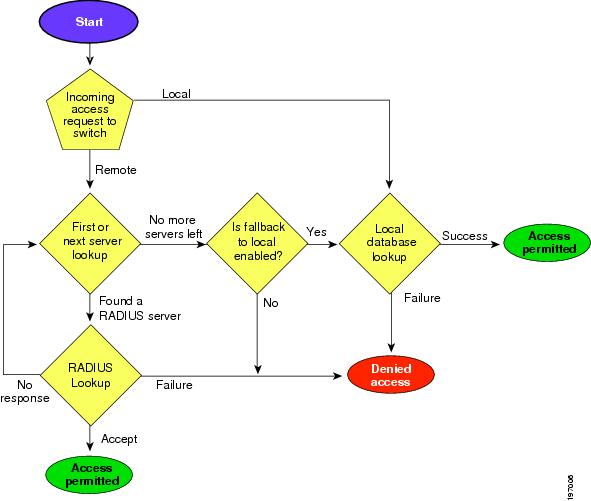
Authorization and Authentication Flow for User Login. This figure shows a flow chart of the authentication and authorization process for user login:
Default AAA Parameter Settings:
| Parameters | Default |
|---|---|
| Console authentication method | local |
| Default authentication method | local |
| Login authentication failure messages | Disabled |
| CHAP authentication | Disabled |
| MSCHAP authentication | Disabled |
| Default accounting method | local |
Process for Configuring AAA
Follow these steps to configure AAA authentication and accounting:
- If you want to use remote RADIUS, TACACS+, or LDAP servers for authentication, configure the hosts on your Cisco NX-OS device.
- Configure console login authentication methods.
- Configure default login authentication methods for user logins.
- Configure default AAA accounting default methods.
TACACS Configuration Example:
- Setup your TACACS+ server group:
aaa group server tacacs+ AUTH_SERVERS
server 10.0.0.5
server 10.0.0.6
use-vrf default
Code language: CSS (css)- Specify the authentication key for each server:
tacacs-server host 10.0.0.5 key 0 AUTH-KEY-HERE timeout 5
tacacs-server host 10.0.0.6 key 0 AUTH-KEY-HERE timeout 5Code language: CSS (css)- AAA Configuration:
aaa authentication login default group AUTH_SERVERS
aaa authorization config-commands default group AUTH_SERVERS local
aaa authorization commands default group AUTH_SERVERS local
aaa accounting default group AUTH_SERVERS local
aaa authentication login console fallback error local
Code language: JavaScript (javascript)- Set the source interface for TACACS+:
ip tacacs source-interface vlan 1Code language: PHP (php)Guideline:
- If you modify the default login authentication method (without using the local keyword), the configuration overrides the console login authentication method. To explicitly configure the console authentication method, use the aaa authentication login console {group group-list [none] | local | none} command.
Reference:
theroutingtable.com/cisco-nx-os-tacacs-setup-guide/
cisco.com/c/en/us/td/docs/switches/datacenter/nexus9000/sw/6-x/security/configuration/guide/b_Cisco_Nexus_9000_Series_NX-OS_Security_Configuration_Guide/b_Cisco_Nexus_9000_Series_NX-OS_Security_Configuration_Guide_chapter_0111.html

![OSPF DR and BDR Election Explained [with Configuration]](https://learnduty.com/wp-content/uploads/2022/03/image-33.png?v=1647900046)
![OSPF Neighbor Adjacency Requirements [With Configuration]](https://learnduty.com/wp-content/uploads/2022/03/image-23-418x450.png?v=1647900064)
![BGP Route Reflector [Explained & Configuration]](https://learnduty.com/wp-content/uploads/2022/02/image-79-531x450.png?v=1647900109)
![Cisco Catalyst 9000 Switches Upgrade [Step by step]](https://learnduty.com/wp-content/uploads/2022/02/image-54.png?v=1647900155)
![L2 Interface Policy – Per Port VLAN in Cisco ACI [Explained]](https://learnduty.com/wp-content/uploads/2022/02/image-42.png?v=1647900173)